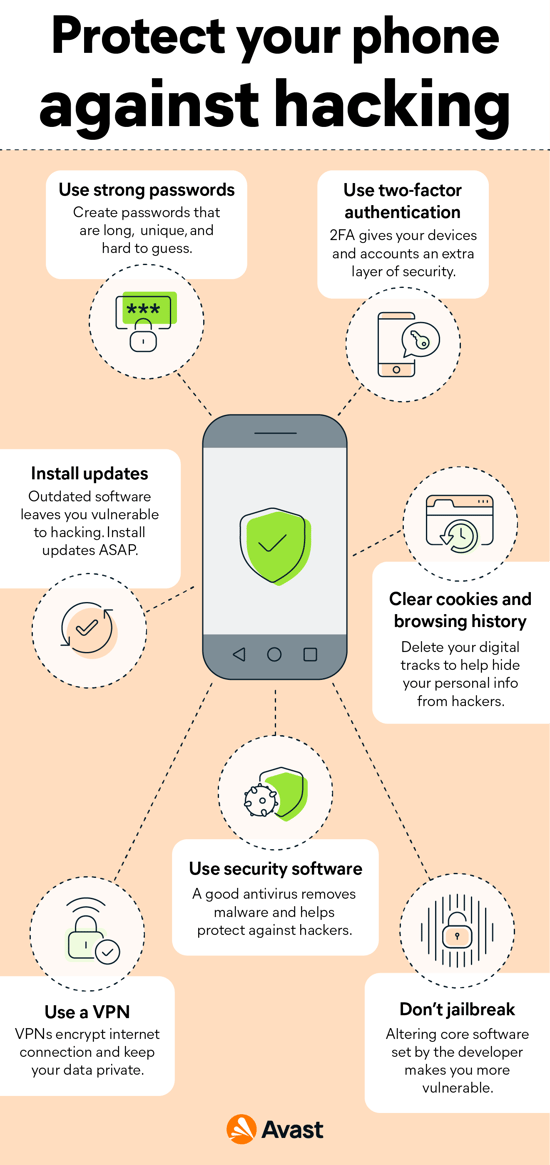
Using TWS or Bluetooth devices? Here's how you can safeguard yourself from Bluetooth hacking - India Today

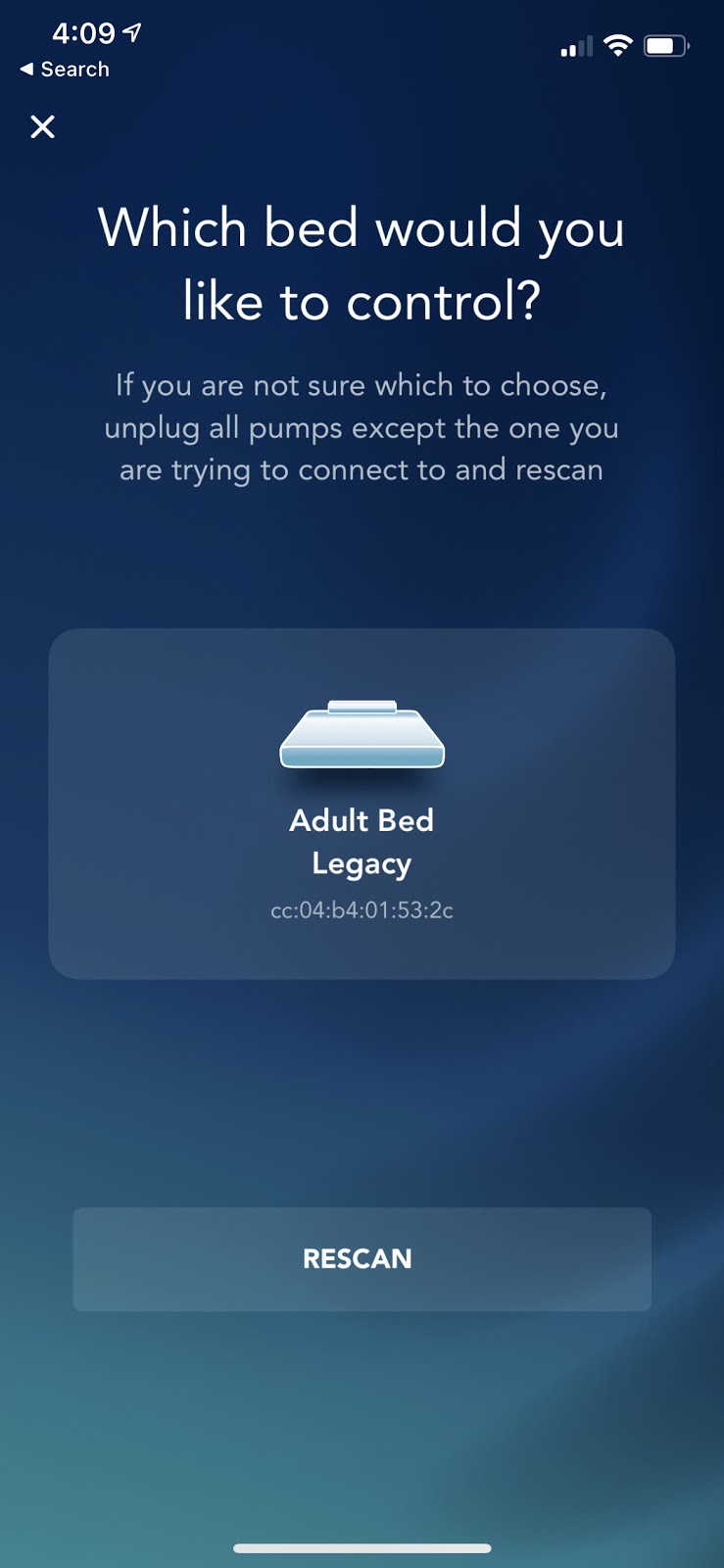
What is a Bluetooth attack? How to safely connect to devices without putting personal information at risk when pairing phone - ABC7 Chicago

Bluetooth güvenlik açığı üzerinden Android, macOS, iOS ve Linux nasıl hacklenir? | Kaspersky Resmi Blogu